RFID technology leads us to a world of connected objects, enabling inventory to speak for its presence and drive processes, as opposed to processes driving inventory. This paradigm shift opens up new avenues and approaches to improving process efficiency, inventory management and business intelligence.
RFID networks enable businesses to build event-driven applications and react to real-time information. If business processes start working with real-time events, enterprises can become more efficient and lean.
|
|
To have a successful RFID implementation and reap true benefits, businesses must first identify business goals, build RFID networks that provide visibility into assets and inventory, and collect RFID data and convert it into actions, perhaps in real time.
An RFID network generates a continuous stream of data. Because of its sheer volume, this data needs to be handled very carefully. In the world of connected objects, the goal is to have efficient RFID networks that provide the right information to the right application at the right time (the “3 Rs”) and make enterprise-management systems event-driven.
Event-Driven Enterprise-Management Applications
For most companies, enterprise resource planning (ERP) systems keep track of the location and quantity of inventory, while supply chain execution (SCE) systems determine how much to produce, where to produce it and how to distribute it. Processes typically control the production and flow of inventory across the supply chain—a process-driven approach. In the world of connected objects, where RFID networks sense the presence (or absence) of inventory, business processes will become driven more by events than by processes. The receipt of a purchase order is an event, and it may trigger several business processes—such as manufacturing and logistics—upon its arrival. A shipment’s receipt may lead to several Electronic Product Code (EPC) reads and trigger an electronic proof of delivery (ePOD) application, as well as updates to inventory counts in a warehouse management system (WMS), and the fulfillment of orders awaiting this receipt of shipment.
This fundamental paradigm shift, in which inventory drives processes, fosters efficiencies in the supply chain (or asset utilization) that could not have been achieved in a process-driven world.
Building event-driven processes is a very challenging task, one that requires a tectonic shift in thinking. It may require defining new processes and retraining personnel. Several technical or engineering challenges arise when dealing with a continuous stream of RFID data where time is an integral dimension. Conventional analytical tools have a hard time harnessing actionable intelligence from such data. The biggest cause is RFID data’s very nature.
Nature of RFID Data
RFID data has some similarities with other streaming data, such as stock trades, but it is still very different.
High volume: RFID interrogators read any tag within their read range, generating a huge amount of RFID events.
Non-contextual: An RFID tag is read as it enters the vicinity of an RFID interrogator, and an RFID event is generated and routed over the network. At the lowest level, the event is just a tag ID, a reader ID and the time last seen. The broadcasting of each RFID event to all parties creates too much noise, however, and not every application needs a particular event. The result is more traffic on the network, and applications get bulkier and slower because they have to process every event.
Spurious reads: Because of the wireless nature of RFID technology, RFID tags are read any time they come within the read range of an interrogator. A poorly tuned reader may pick up tags that are far away. If the receiving and shipping portals are close and a tag passes through the receiving portal, a spurious EPC read may occur at the shipping portal as well. Spurious reads can also happen due to human error. A forklift carrying RFID-tagged inventory may take a wrong path, for instance, resulting in spurious reads. From an application standpoint, such reads need to be discarded by putting business rules or appropriate checks and balances in place.
Non-transactional reads: If a forklift carrying tagged material passes through a reader’s vicinity three times, three different events are generated for the same tag, even though only one is relevant to the application. This might happen if an operator were to overlook something and back up the forklift to correct the mistake. Two of the three resultant reads would be spurious and would need to be discarded, either by the network or by the applications consuming the data. The later choice would increase traffic on the RFID network. Applications need logic to sieve out such spurious events, making them bulky.
Short life: RFID data becomes obsolete quickly as a tag moves to the next stage in a business process. If the finished product is shipped out of a factory, the complete history of that tag may be moved to an archival database, or even discarded (as opposed to keeping it in the active database and increasing the cost).
Converting RFID Data Into Information
The volume of RFID data makes it imperative to handle that data very carefully, at the proper time and the right place in the RFID network. The main difference between data and information is that information has a business context associated with it and is valuable to certain processes or applications with minimal interpretation.
Consider the example of receiving RFID-tagged goods at a receiving dock door. As an RFID interrogator receives inventory, many RFID read events are generated. Raw RFID data consists of individual RFID reads, stored as separate events in the repository. If all these EPC reads were collected and compared with an advance shipping notice (ASN), that would translate to more meaningful information. These multiple RFID reads could be stored as a single business event, called “receiving,” which would then be more relevant to the business. This business event, “receiving,” would be transmitted to a receiving application, such as ePOD, to send out notifications to the sender of those tagged goods.
In a supply chain dealing with perishables, a business event called “stale” would be very helpful, compared with just a raw RFID read. As an EPC was read in the supply chain, the RFID network could evaluate the freshness of the product using master data. If the EPC were read past the expiration date, then a business event called “stale” would be stored in the RFID network. Anytime this EPC was read again in the supply chain, the RFID network would look for a stale event and stop the product from going further without any additional evaluation.
A single physical read may lead to multiple business events. To turn RFID data into meaningful information, one needs to convert and authenticate it into events using business rules, store business events (such as “receiving” or “stale”) and route them to the right application.
Event Routing
An RFID network may generate high volumes of streaming RFID reads, while subscriber applications may receive RFID reads in two ways:
• Every EPC (or auto-ID) read is sent to all subscribers of an RFID network.
• Subscribers receive only processed events they have requested.
Comparing this with Internet Protocol (IP) networks, the first strategy is similar to a hub, where all IP packets are broadcast to every device connected to that hub. In an RFID network, this strategy creates unnecessary traffic and puts the burden on the applications to sieve out the “interesting” events. In a smart RFID network, raw events are pre-processed and converted to business events before being passed to the subscriber applications. As information flows in a company’s RFID network, it may change its form and content.
Application-Driven Smart RFID Networks
Data becomes valuable information if it is relevant to a recipient. In an application-driven RFID network, applications define the rules for processing RFID reads. The network layer executes those rules for organizing RFID data and then delivers quality information to its subscribers. The most common example would be an RFID network providing a location service. Anytime an application needed to know the last location of an EPC, it could query the RFID network to obtain it. This service could help with recall management or just-in-time replenishment if one knew how far the inventory reached in the supply chain.
Similarly, a smart RFID network can provide other services, such as dwelling times at a particular location, or the transit time between two locations. RFID networks can also provide complex services—for instance, “no product received (at a location)” or “no product stocked. “This service can help monitor promotion execution in the retail supply chain, or ensure customer satisfaction in any supply chain. Another example of complex service would be pushing alerts out to subscribers when an inventory is aging or has already reached the stale status.
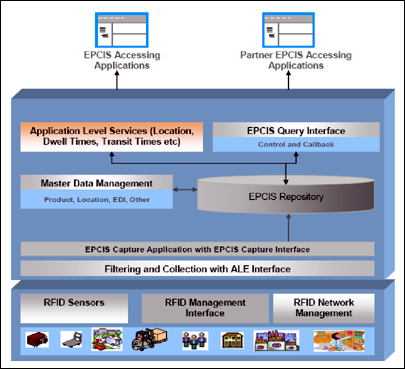
Smart RFID Networks hide the complexities and limitations of RFID technology, while providing the right information to the right application at the right time. The topology of RFID interrogator networks depends upon the tracking and tracing capabilities needed to achieve enhanced process efficiency, better inventory control and improved business intelligence. The software stack of the EPC network consists of two distinct layers: namely, filtering and collection data using an Application-Level Events (ALE) interface, and EPC Information Services (EPCIS) with enterprise applications or with partners. The middle step of converting RFID data into information is vital for successful RFID network implementations, because of the sheer volume, granularity and nature of RFID data.
The cost of harnessing business intelligence increases as RFID data moves closer to applications. The implementation of RFID networks driven by target applications will lead to better business intelligence, faster and cheaper event-driven enterprise applications and more manageable and sustainable software architecture. Smart RFID networks can provide such application-level services as location, dwell times, transit times and quantity, and also issue alerts when exceptional situations—stale and aging inventory, for example—are detected.
Hersh Bhargava is the founder of RafCore Systems. He is the visionary behind the company’s mission of enabling enterprises to respond in real time using the automatic data collection techniques that RFID provides.