As radio frequency identification tags wend their way into more consumer applications—from access cards to payment devices, library cards, passports and clothing—privacy advocates, politicians and, increasingly, consumers are crying “foul.” But as concerns grow that RFID tags are susceptible to skimming—being read surreptitiously—or being used for surveillance, so do efforts to safeguard RFID tags in order to prevent data from falling into the wrong hands. Some of these efforts—such as encryption techniques that ensure tags can be read only by authenticated readers—are still in the preliminary research stage. But other technology tools are available today, as are some low-tech tag protectors (see box).
The security firm Privaris makes a device called plusID that uses a biometric lock to prevent someone from using your access card or reading your ID and cloning the data onto another device. To gain entry with plusID, you have to press your finger on the device’s integrated fingerprint reader. A processor inside the device compares your fingerprint scan with one saved in its onboard memory. If it matches, it enables the tag inside to be read. PlusID, which is small enough to add to a keychain, works with most access control systems that operate in the 125 KHz or 13.56 MHz frequency range. It is being used by a number of companies and by military personnel at high-security facilities.
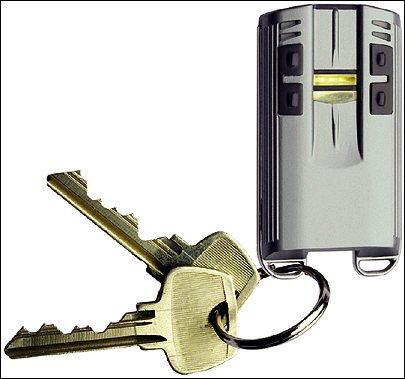
Raytheon, a government defense, aviation and technology company, has recently unveiled a prototype of a device called the PAD (personal authentication device), which is very similar to plusID, except that it has a UHF EPC Gen 2-compliant tag. Raytheon is proposing that the PAD be issued to U.S. citizens as a biometrically verifiable identity card for various Department of Homeland Security initiatives.
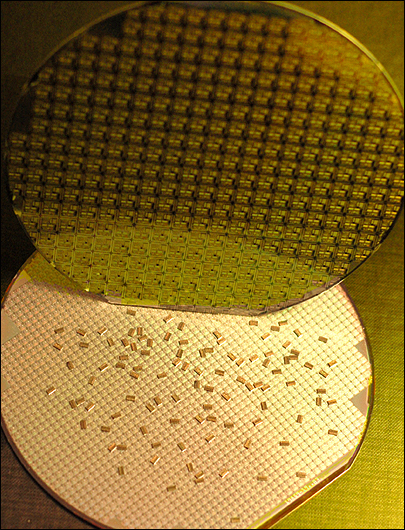
RFIDsec, an RFID startup, has developed an RFID security system that consists of specially designed tags and interrogator software, which uses a 128-bit key to place the tags in an unreadable privacy mode. The company says it has built the technology into HF tags—commercially available in July—compliant with the ISO 15693 and ISO 14443 air-interface protocols. The RFIDsec tags could be embedded in access control, identification and payment cards, as well as in labels that libraries place inside books. “We are running live demonstrations [of the HF tag] already and running a pilot project with a large library,” says Mikkel Winther, executive vice president at RFIDsec.
The company is looking for business partners to help fund its effort to develop the system for UHF Gen 2 tags and interrogators, which would provide an alternative to killing product tags at the point of purchase. In order to provide the privacy-mode service to consumers, companies would need to run the RFIDsec software on their reader networks. But RFIDsec imagines that one day consumers will carry their own RFID interrogators on which they could run the RFIDsec application to control the readability of tags in their possession.
The RFID Guardian, being developed by researchers at Vrije Universiteit (Free University) in Amsterdam, could allow consumers to do just that. The Guardian uses a set of digital keys to permit or restrict RFID tags from being read, just as firewalls permit or deny entry into a computer network. The device reads the RF communication from an interrogator and checks the signal for a digital signature, or key, signifying it is authorized. If the Guardian sees the key, it allows the tag to be read. If the interrogator is not using an authorized key, the Guardian emits a jamming signal, preventing the interrogator’s signal from reaching the tag.
Consumers could also use the device to run audits to see which of their tags—such as those embedded in identity documents or access cards—have been read throughout the course of a day, along with a record of when each was read. Melanie Rieback, a doctorate student at the school and one of the lead Guardian developers, says the group plans to refine the prototype device by adding Bluetooth capabilities, streamlining its size and adding a rechargeable power source.
The device works only with HF ISO 15693 and 14443 tags, used in access, payment or ID cards, but the team plans to develop a UHF version for tags likely to be embedded in consumer products. She says a large chipmaker could boil the components used by Guardian into a form factor small enough to integrate directly into cell phones and PDAs.
IBM has taken a different approach to protecting consumers’ privacy. IBM researcher Paul Moskowitz designed a UHF RFID tag that supports the many feet of readability required by supply-chain applications. But once a tagged item is purchased, you can simply remove a large portion of the tag’s antenna, which reduces the read range to just a centimeter or so.
The tag could still be used for product return verification or warranty claims, which isn’t possible when tags are permanently disabled, or “killed,” at the point of purchase. IBM has licensed the clipped tag to Canadian tag converter Marnlen, which is currently supplying a limited number of the tags to a garment maker using them in a pilot program, but the converter says it can produce the tag in large quantities today.
Who’s Who in Privacy RFID Products
IBM
www.ibm.com
Marnlen
www.marnlen.com
Raytheon
www.raytheon.com
RFIDsec
www.RFIDsec.com
RFID Guardian
www.RFIDguardian.org
Privaris
www.privaris.com
Low-Tech Protectors
RFID-blocking wallets and wallet inserts protect personal information in RFID-enabled access cards, passports and payment cards by shielding the RFID tags so they can’t be read. The data protectors are available from these companies:
Emvelope
www.emvelope.com
DIFRwear
www.difrwear.com
Kena Kai
www.kenakai.com
Skim Block
www.orient-computer.co.jp/ english2/products/en_skim.htm

