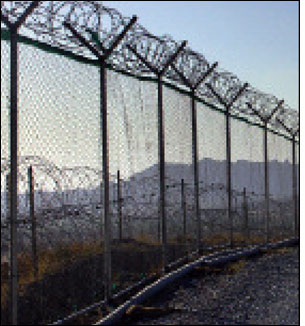
Detecting when an individual or a group illegally enters a chemical factory, oil refinery, nuclear power plant or military facility is critical. Conventional perimeter intrusion-detection devices typically consist of cables, attached to fences, that sense vibrations, cuts or acoustic changes. But terrorists can get around these systems by building bridges over them or digging under them. Radio frequency identification just might be a better bet.
Inventor Kenneth Cecil has patented an RFID detection system comprising ultrahigh-frequency (UHF) RFID transponders placed on a wall or fence about two feet apart at varying heights. UHF readers are positioned 30 feet (10 meters) apart, 10 to 20 feet from the tagged wall, and set to ping the tags 20 times per second.
The system also includes controllers designed to reside in the field and connect with up to 30 RFID readers. A central monitoring controller, at a remote location such as a guard station, continually polls all field controllers. When a transponder fails to respond, the field controller reports the transponder’s unique identification code to the central monitoring controller, which has a database of tag IDs linked to specific locations, to determine where the breach occurred. The central monitoring controller also manages the alerts.
The body of someone attempting to scale a wall or tunnel under it absorbs the RF energy between a tag and a reader, briefly blocking the signal and preventing the tag from responding to the reader with its unique ID. The field controller relays the tag’s unique ID to the central monitoring controller. You can also set the system to send an SMS (short message service) text message to a security guard’s phone, point a closed-circuit TV in the direction of the intrusion, sound an alarm or all of the above.
“I developed a prototype and tested it,” Cecil says. “The system is very simple but very effective. We will start production soon.” Integrated Security, of Walled Lake, Mich., will distribute the product in the United States, he notes.
Cecil has also developed a tunnel-detection system that involves burying RFID tags and readers in plastic pipes and monitoring interruptions between signal and tag. If the solution catches on, maybe we’ll all sleep more soundly at night.