The Internet of Things (IoT) encompasses a wide range of devices, from connected refrigerators to insulin pumps. It has also been a popular solution for enterprise executives looking for ways to increase the quantity and quality of information about their businesses. The prevalence of these connected devices that line not just our homes, but also countless enterprises across all industry verticals, makes IoT vulnerabilities extremely target-rich and, therefore, incredibly attractive to hackers. And though a vulnerable smart toaster may not culminate in debilitating repercussions for our connected world, the rise of smart infrastructure and autonomous vehicles means that software security will soon be synonymous to the safety and privacy of all.
Is Open-Source Critical in the IoT?
We are developing, sharing, and adopting open-source software (OSS) at an unprecedented rate. A 2018 audit by OSS risk-management market leader Synopsys revealed that in just a span of one year (from 2017 to 2018), the average percentage of codebase that was OSS jumped from 36 percent to 57 percent, indicating that many applications now contain more open-source than proprietary code. The IoT industry is no exception. According to the same audit, open-source code comprises an average of 77 percent of scanned IoT codebases, demonstrating that this industry is built upon the foundation of OSS. This trend will only continue to grow because, by leveraging OSS, development teams can lower assembly costs and quickly add innovations, thereby saving months or years of originally required development time.

But OSS is not perfect. Whether software code is proprietary or open-source, it harbors security vulnerabilities. Supporters of open-source argue that the accessibility and transparency of the code allow the “good guys”—corporate quality-assurance teams, white-hat hackers and open-source project groups—to find bugs faster. Yet the same accessibility and transparency that make open-source so valuable also equip hackers with ready-made lists of security vulnerabilities that they can exploit if IoT OEMs and their third-party development teams have not fixed their software.
Is Our Connected World Secure?
The combination of the prevalence of IoT devices and heavy usage of OSS in this industry should warrant constant vigilance to ensure that these connected devices are secure. Yet recent events indicate that negligence rather than vigilance has been a recurring theme for IoT security. A vulnerability in a third-party open-source project named gSOAP, later called Devil’s Ivy, was exploited by hackers to remotely access a video surveillance feed while denying the owner access to the feed. The fragile security of these connected home devices even prompted the FBI to issue “privacy and physical safety” warnings for smart toy sensors such as microphones, cameras, and GPS (see FBI to Parents: Beware, Your Kid’s Smart Toy Could Be a Security Risk).
At Black Hat 2017, two security researchers demonstrated their ability to hack internet-connected car washes. They were able to close the entry and exit doors, thereby trapping the car and its driver, and remotely maneuver the car-washing apparatus to strike the vehicle. The hackers could stop the driver’s attempts to escape by repeatedly opening and closing the doors, further damaging the car and potential injuring the occupants. In the same year, St. Jude Medical’s cardiac device implants were revealed to contain vulnerabilities that hackers could use to tamper with the device’s control of vital heart functions. St. Jude’s failure to remediate the “universal code that could allow hackers to control the implants” invited the criticism of investment firm leader Carson Block, who threatened to short-sell the device’s stock.
While some organizations fail to prioritize IoT security, more security-conscious companies leverage specialized security solutions to identify and manage the relevant issues in their codebase. Some choose to deploy software composition analysis (SCA) tools developed by security technology innovators such as Synopsys and Insignary, which equip customers with customized security reports so they can practice effective OSS risk management. But this is not an be-all and end-all solution.
To produce these reports, SCA tools leverage external databases of known OSS-related vulnerabilities, against which they map the customer’s individual risk. Yet these databases are limited by their centralized management, which hinders them from addressing the escalating number of OSS projects and associated security risks. As a result, the information found in these databases is neither complete nor up-to-date, preventing organizations from remediating security vulnerabilities as efficiently and effectively as possible.
A Flawed Reporting System
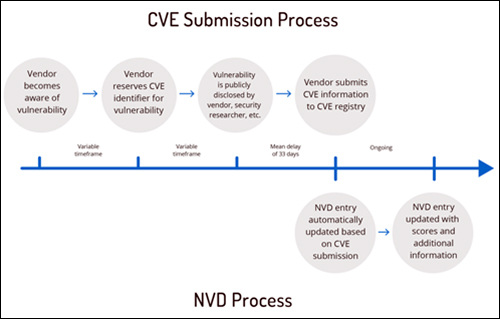
The most popular centralized vulnerability database is the National Vulnerability Database (NVD), a public database funded by US-CERT, an organization within the US Department of Homeland Security. Central to the NVD’s vulnerability reporting process is the Common Vulnerabilities and Exposures (CVE) reference-method system, which assigns each publicly disclosed security vulnerability with a CVE identification number. CVE IDs are assigned by the CVE Numbering Authority (CNA), and are used for communication between software development teams and researchers, vulnerability disclosers, and information technology vendors.
The CNA comprises a group of fewer than 100 qualified organizations that boast a global reach and include impressive names, such as Google and Microsoft. However, the centralized nature of the CNA’s management means that vulnerability reporting is oriented toward security issues specific to products managed by organizations that comprise the CNA. Google will focus on finding potential security vulnerabilities in the software used to build Google products, as will Facebook and Microsoft. However, many OSS projects, including those that are critical to the IoT industry, do not have this corporate sponsorship, are left underserved as a result of this bias in the vulnerability reporting process.
Vulnerability Inclusion Time Lag
The CNA’s closed management also results in a significant time lag between the first discovery of a vulnerability and the publication of this vulnerability on the NVD (see The Race Between Security Professionals and Adversaries). Recorded Future, a Boston-based security research firm, discovered that out of 12,517 observed vulnerabilities, open, deep or dark web coverage revealed 75 percent of these vulnerabilities prior to their inclusion on the NVD. The firm reported an average of 33 days between the initial announcement of the problem and its subsequent publication on the NVD. This time lag presents a huge problem, as it not only slows down the response time of support organizations to address gaps, but also extends the window of opportunity during which malicious actors can hack both enterprise servers and personal devices.
In comparison to NVD, China’s National Vulnerability Database (CNNVD) demonstrates better efficiency in reporting vulnerabilities, with an average of 13 days between the first reporting of a vulnerability and its inclusion in the database. Thanks to this shortened time lag, the CNNVD houses more up-to-date information about software vulnerabilities than does its U.S. counterpart on any given day. But this is still far from optimal.
Information Manipulation and Withholding Cause Cybersecurity Issues
The government-sponsored nature of these publicly available databases prompts open questions about whether the authorities maintaining these databases are motivated to freely share all the information that they collect. The National Security Agency (NSA), in particular, has been known to keep vulnerabilities secret for espionage purposes, rather than disclosing them. This prevents the relevant system and device manufacturers from addressing their problems to protect the greater public (see Why Governments Won’t Let Go of Secret Software Bugs).
The tampering and retention of vulnerability data is not limited to platforms connected to the U.S. government, The CNNVD has a track record of original publication dates of vulnerabilities in attempts to conceal which vulnerabilities China’s Ministry of State Security may leverage and to prevent external researchers from predicting Chinese advanced persistent threat behavior (see China’s National Vulnerability Database Is Merely a Tool for Its Intelligence Agencies). In addition, by eliminating the publication lag of these security risks, the Chinese government aims to hide the fact that they withhold a selection of high-threat vulnerabilities that could be useful in advancing national security goals (see China Altered Public Vulnerability Data to Conceal MSS Influence).

Clearly, existing centralized security databases cannot provide us with the visibility needed to secure our IoT infrastructure and mitigate cyberattacks. We must stop relying on these deficient options and instead develop a timely, transparent, and well-resourced system for reporting and recording security vulnerabilities critical to IoT software.
Using Blockchain and Cryptocurrency Platform to Address These Issues
We must develop a new, secure model that is committed to the free flow of information about vulnerabilities, so we can address known security threats as quickly and efficiently as possible.
This new approach resolves the issues of the current model by doing the following:
• Building a decentralized database of OSS vulnerabilities managed by multiple independent entities with an inherent system of checks and balances to assure a free flow of information;
• Securing this database with blockchain technology to prevent data manipulation and ensure participants are in-sync;
• Incentivizing OSS communities with tokens to crowdsource the reporting and verification of vulnerabilities, thereby increasing both the number of contributors and their participation;
• Prioritizing OSS projects critical to IoT security to ensure contributor activity in segments of the OSS market without corporate sponsorships; and
• Creating an independent economic system which sustainably pays for the operation of the platform.
Blockchain-based Vulnerability Information Platform
The first step in creating this new, open model would be to build a vulnerability database that is operated and maintained by a decentralized, global group of interconnected autonomous stakeholders. These stakeholders would be driven to manage the platforms in order to access a definitive source of truth about vulnerabilities, but their costs to operate and maintain the database would be offset by a distributed token-based price model offering access to the entire database. The new security vulnerability knowledge base would leverage blockchain technology to secure the integrity and immutability of the stored information.
The More Eyes, The Better to See
A token system would be used to reward the operators of the nodes participating in vulnerability tracking platform. Tokens would also be used as a “bug bounty” to incentivize and crowdsource the finding and reporting of potential OSS security issues, thereby continuously populating the database. The smart contract for the bug bounty program would execute when a vulnerability in an OSS project is verified by the OSS community. Tokens could also reward verifiers for correctly validating the reported security vulnerability. This new tokenized incentive model can counterbalance the currently disproportionate amount of contributor attention given to sponsored and high-profile OSS projects.
Moreover, by rewarding users with cryptocurrency rather than fiat currency, the vulnerability tracking platform can eliminate currency exchange fees—a valuable factor for contributors residing in developing countries.
Prioritizing IoT Security
We expect to see 20.4 billion IoT devices by 2023. With billions of data collecting IoT devices controlling and monitoring our cars, homes and even health functions, it is crucial to maintain IoT device security in order to prevent the likes of identity theft, privacy breaches and public safety accidents.
Consequently, this new model of vulnerability reporting and recording should prioritize security issues associated with OSS projects critical to the IoT industry. It can leverage the aforementioned software composition analysis tools developed by companies like Insignary and Synopsys to gain an understanding of which OSS projects are heavily leveraged by IoT device manufacturers and software developers. The platform can then assign higher token value for vulnerabilities found in these pre-identified OSS projects, incentivizing market resources to focus on reporting and verifying these target-rich security flaws.
Paying for Usage of the New Vulnerability Database
Currently, individuals and organizations can use public databases such as NVD and CNNVD, free of charge. However, the aforementioned deficiencies found in these options may prompt medium and large corporations to purchase access to commercial alternatives, such as VulnDB. Though superior to publicly available versions in their breadth and timeliness of information coverage, commercial databases are often very expensive, and are therefore financially infeasible for smaller companies.
Consequently, this new security knowledge base should employ two pricing models. The first option would target large enterprises that plan to check the database on a regular basis as part of their DevOps process. These organizations could pay an upfront fee for unlimited access to the database. The second option would be a pay-as-you-go model designed for smaller companies that do not need to use database as often. Since the new system would run on cryptocurrecy, smaller companies would have the option to pay for access to the database by earning tokens through participation in the reporting and verification of security vulnerabilities.
A Better Way Forward
Security breach after security breach, we are constantly reminded of our lack of awareness of OSS usage and the inadequacies of current centralized vulnerability tracking and mitigation options. These deficiencies, such as time delays, information omission, and uneven participation among OSS projects, prevent device manufacturers and software developers working in the IoT space from promptly addressing software vulnerabilities that could endanger their direct users and the general public.
There is a need to develop a more robust and effective alternative through a decentralized system of vulnerability reporting and mitigation that leverages cryptocurrency and blockchain technology. By planting more eyes in the OSS security community with tokenized incentives, this new, self-sustaining platform of decentralized vulnerability reporting will dramatically improve the security of the IT infrastructure on which everyone relies.
Tae-Jin (TJ) Kang is a technology industry executive and entrepreneur. He is the CEO of Secure Planet. In addition to founding a number of successful technology startups, TJ has held senior management positions with global technology leaders that include Korea Telecom and Samsung Electronics, among others.

