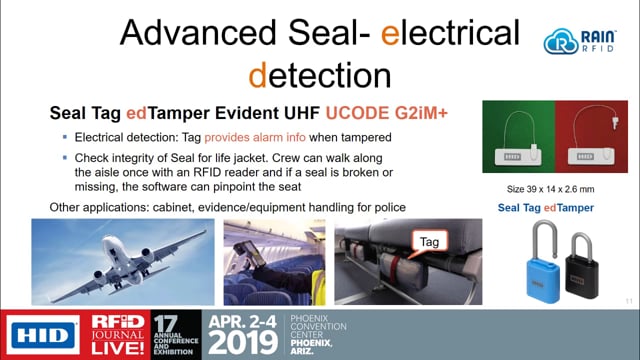
As RFID and BLE technology is increasingly adopted across a number of scenarios, it turns out that a number of these use cases require a higher level of security. The tags and the affixed items must stay together and that identification tag or sensor cannot be cloned. This session will describe several physical, cryptographic and RFID aspects of implementing tamper evidence in RFID tags and describe related real-life implementations.
Speaker:
Richard Aufreiter, Director, Product Marketing, Identification Technologies, HID Global