by Admin | Jun 13, 2018 | News
The growing number of Wi-Fi-connected shadow devices, both those provided by an employer and personal devices carried by workers, are raising threats for cyber-attacks, the report indicates.

by Admin | Jun 12, 2018 | Expert Views
With an RFID-enabled tracking system, the entire relocation process, from planning through execution to completion, becomes smoother.

by Admin | Jun 12, 2018 | News
The Annihilyzer solution, from Paradigm Convergence Technologies, leverages hydrochlorous acid to kill germs without toxins, while RFID tracks its 30-day shelf life to ensure it’s being used properly.

by Admin | Jun 11, 2018 | Editor's Views
Some software providers are promising to improve retailers’ inventory accuracy. Here’s why algorithms alone won’t work.

by Admin | Jun 11, 2018 | News
Powercast’s new Batteryless Electronic UHF Retail Price Tag receives pricing information from an RFID interrogator, while also harvesting the RF energy, then uses that energy to change the price accordingly on its display.

by Admin | Jun 10, 2018 | Expert Views
How to manage the influx of IoT data to improve your product.
by Admin | Jun 8, 2018 | News
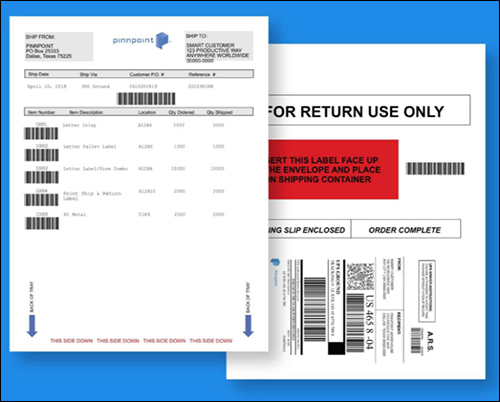
The resultant on-demand printing solutions allow shippers to automatically view the status of returned goods via RFID tag reads, enabling the growing reverse logistics model for online shopping.
by Admin | Jun 7, 2018 | News
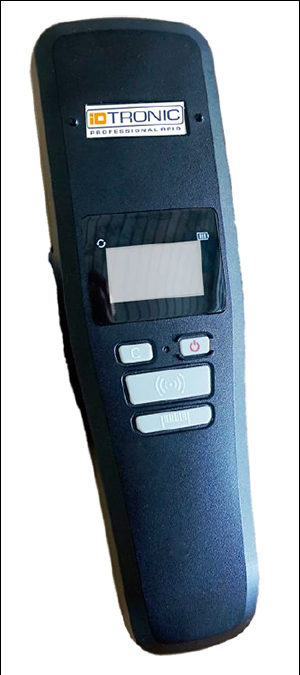
Wade Garcia & Associates, InCom enter licensing agreement for RFID attendance-taking system ••• iDTRONIC releases new handheld RFID computer ••• STMicroelectronics’ NFC technology powers new TCL communication smartphone ••• Balluff magnetic mount simplifies RFID integration ••• Electric Imp intros cellular IoT service ••• Quuppa to host partner event for indoor location services.
by Admin | Jun 7, 2018 | News
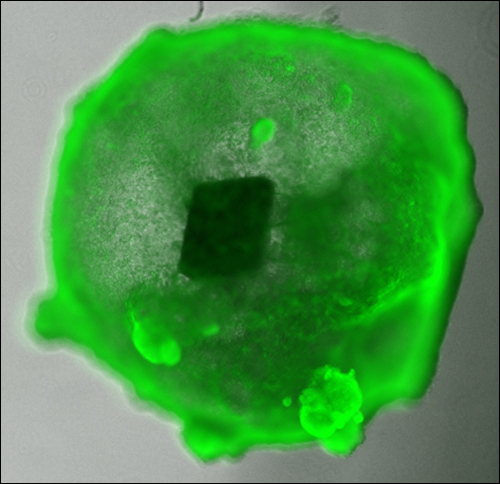
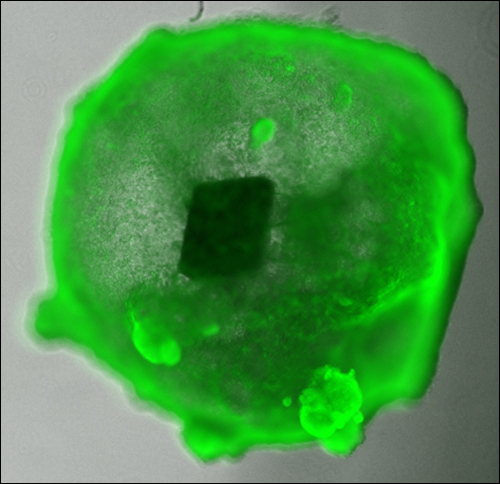
Researchers at Cincinnati Children’s Hospital have conducted a test of their UHF RFID-enabled miniature human organs to enable high-volume testing of the tissues in pharmaceutical and implant development.

by Admin | Jun 6, 2018 | Expert Views
Security at the process level is essential to creating an immunity to the cyberattacks of tomorrow.